Uma Iyer critiques the efficacy and ethicality of digital era marketing ploys that lure unprepared consumers into their traps
I was speaking to a friend about the Maldives getting submerged in the next ten years due to global warming and why I really need to start planning the visit soon. Lo and behold, I get feeds on my Facebook page about trips to Maldives! I did not search, but I merely said Maldives! Then I was thinking about a tennis holiday, I didn’t even say it, but I see tennis holidays on my feed! Are the devices in my house now reading my subconscious thoughts? Although that may seem like a far fetch, somewhere, something I did on my digital footprint may have led to data that then helps the targeted marketing vendors!
Sify Technologies – Digital Services
Did you know that Mark Zuckerberg puts a blue tack on his video camera on the laptop? Why does he do that? Are we being seen without our permission using our devices even?
The use of systems in daily use is staggering
How does it actually work?
Social media applications and Website cookies are the most popular and easiest way of capturing leads and sale conversion. However, the more predominant ones are also Voice enabled devices.

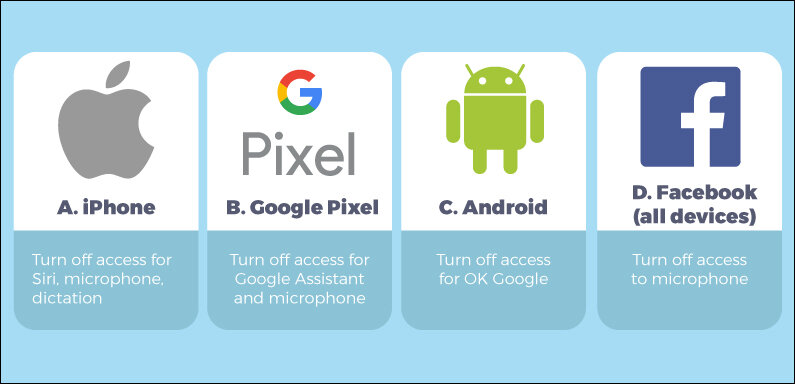
Do Apple/Siri’s/Google’s/Facebooks contribute?
Apple in August 2019 apologized for its “Siri grading program” which allowed contractors to listen to a small percentage of things people spoke. Apple then said that they will enable a few changes that gives users more control with how the voice enabled program will work. However, it is pretty clear that many of the users are unaware of such settings and inadvertently party to many of these experiments or marketing strategies.

- Alexa: While claims are that the ‘wake’ word Alexa needs to be triggered to detect, there is no guarantee that it is indeed true. Alexa performs a “cloud verification” to confirm its detection. The policy however is unclear on what happens to the audio received if the wake word is not verified or incorrectly verified by Alexa.
- Google Assistant: As per Google’s policy, the device activates only upon hearing words like “Hey Google” or “Ok Google.”. It is said that Short snippets of audio (a few seconds) are processed to detect an activation and audio snippets won’t be sent or saved to Google if that is not the case. The policy is again unclear on how the activation word is detected and where the short snippets are processed for learning purposes.
- Siri: Activated by voice by using the words, “Hey Siri.” the policy is completely silent on how it processes the activation word. The policy also states that transcripts of voice recordings are always sent to Apple servers. Therefore, in cases of false detection of the activation word, even if the audio is processed on the device, processing and storage of transcripts on servers will still take place without user knowledge.
How do advertisers and marketers hook in?
The big players now are Artificial intelligence and machine learning. They all work together to target ads efficiently. Online Marketing tools are used to automate processes and reduce errors. Each channel has specific algorithms to identify the best time, size and type of ad to help maximize sales.
Why is “Eavesmining” dangerous?
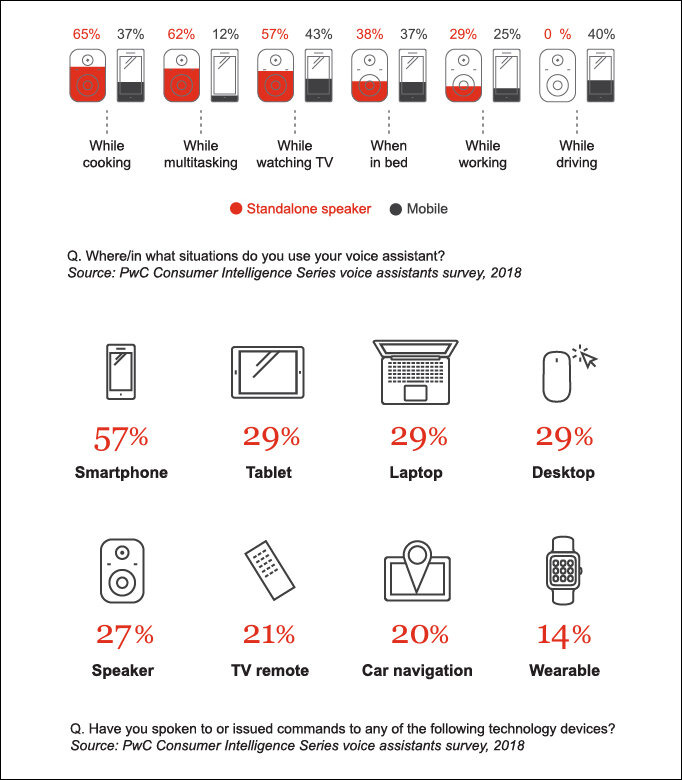
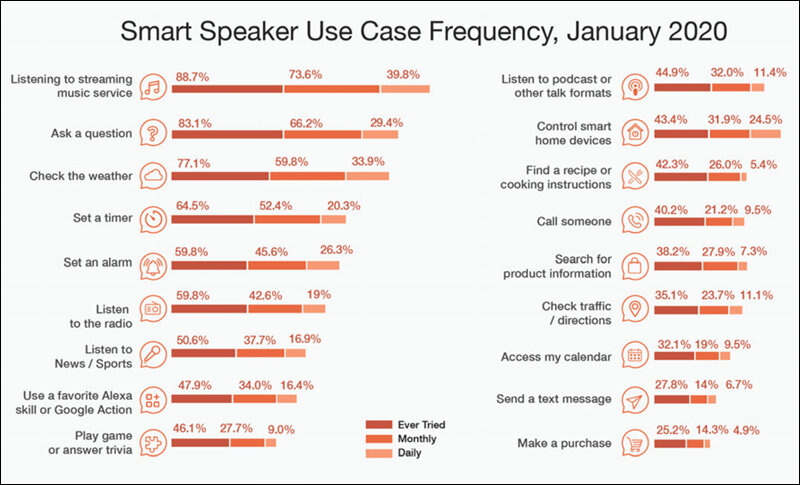
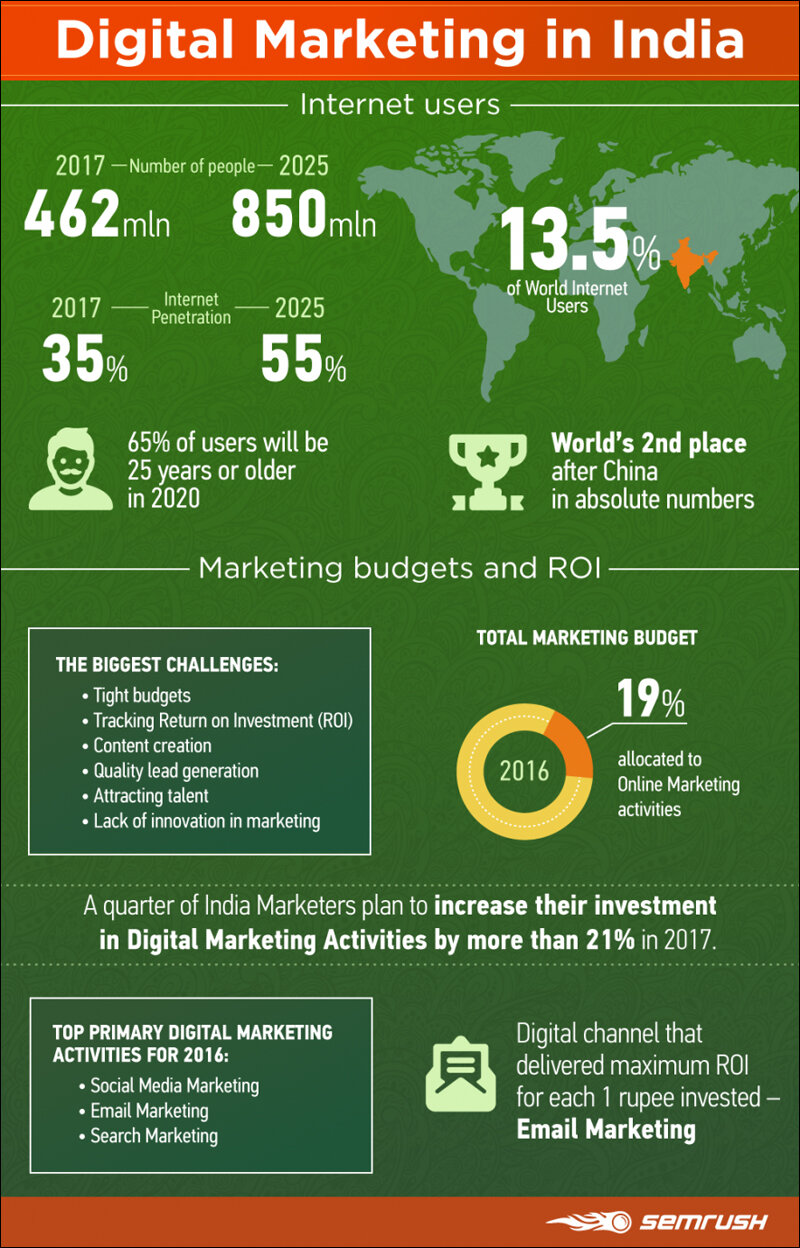
India is witnessing a 270% year-on-year growth in voice searches. In 2020, 60% of users in India were estimated to be interacting with voice assistants (‘VA‘) on their smartphones. The Mobile Marketing Association in its ‘The Voice Playbook‘ (2021) records that smart speakers are being used on a daily basis for listening to music, asking questions, checking the weather, setting a timer, setting an alarm, listening to news and so on. The report points out that the reason for such exponential growth may be convenience (voice is faster than typing) and lack of literacy in India which prompts the rural population to use VAs. Mark Weiser who headed Xerox PARC labs explained it well when he stated that, “The most profound technologies are those that disappear. They weave themselves into the fabric of everyday life until they are indistinguishable from it.”
Source: Brand Equity
The voice assistants are listening, processing and also help evaluate the platforms and processes that impact the sonic lives of children and families. Although the idea of phones listening in to our conversations might be a conspiracy theory. Customers are on high-alert shows just how high expectations are when it comes to privacy.
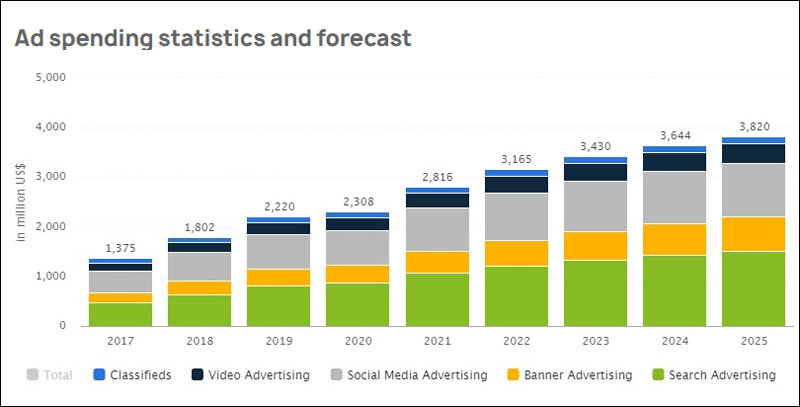
Staggering data on marketing
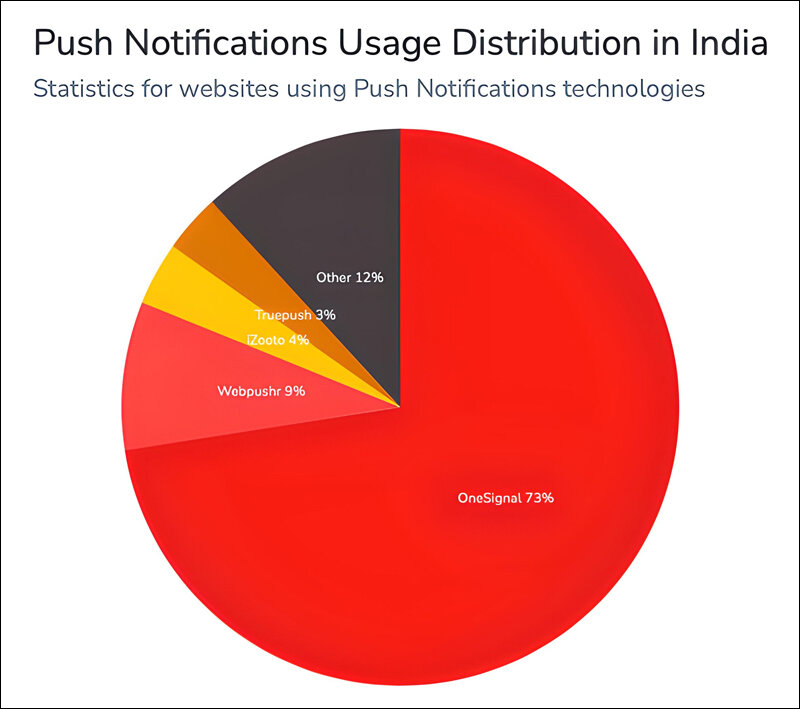
There are around 1 billion clicks daily only with web push ad format. Traffic costs are low for India. For $1 you can buy 100K impressions or 200 clicks, depending on the payment model you choose.
Total clicks daily: 949K
Desktop Users: 8.6K
Mobile Users: 938K
Tablet Users: 2.3K
Mobile Android Users: 940K
This data is current as of December 29, 2020.
Source: ClickAdilla
Spend vs Benefit
Data Brokers specialize in collecting data around what is being bought, what’s read, what engagement metrics are used, what people say to target ads effectively.
Personal Data like identifiable information of Location, phone, address, IP (Internet Protocol), devices coupled with Engagement data with the social media websites or emails can seem harmless. However, behavioral data and attitudinal data can be used against people and used for hate speech and mob bullying.
There is an increase in malware attacks and hacking against voice automated devices are becoming more sophisticated. E.g. Remote execution of voice commands on Alexa which can enable a malicious user to make online purchases with another user’s device. Phoneme morphing is where a device is tricked into thinking a modified recording of an attacker’s voice is the device’s registered user, and ‘dolphin attack’ in which inaudible voice commands can be used to communicate with devices, evading detection by human hearing. These attacks allow the extraction of personally identifiable information from unsecured devices with ease.
Source: ncbi.nlm.nih.gov
Whether its ads clicked through platforms, personal details or information already available or just a simple like, AI (Artificial Intelligence) algorithms can help marketers take huge pools of data and use them to construct your entire persona. It not only is limited to you but also ranking people around you based on how much you “care about” them. This can easily snowball into data collected from friends, family as well. With over 374 million smartphone users which is about 13.8% of the world market, it is an enormous opportunity for businesses.
Why does it need to be regulated?
It is well researched that a “Like” or a “Love” on a post triggers dopamine centers. It is a reinforcement, reassurance and reward that you are attracted to a post. And also brand ambassadors are evaluated on the same. If you start actively liking posts about “mindfulness” on a social platform, the system begin to send you advertisements for companies that offer “Wellbeing” products.
US: Countries like United States have specific data protection laws called Health Insurance Portability and Accountability Act of 1996 (HIPAA), which protects a patient’s health information, Children’s Online Privacy Protection Rule (COPPA), which protects the privacy of children below 13 years old but the privacy laws are still catching up.
Philippines: A stark difference is in countries like the Philippines which have pretty strict data protection laws. So it’s no surprise that it also takes a strong stance against companies that violate these laws. The Philippine Data Privacy Act (PDPA), sets clear guidelines for how personal information is collected, stored and used by companies who collect this information from Filipinos.
Where does India stand?
EU: European union also have very strict data protection laws like the General Data Protection Regulation (GDPR). GDPR protects personal data and requires that companies give people clear information on how they collect, store and use personal data. It also requires them to get consent from users before they do so regardless of their size. This applies to all the companies that are based out of the EU but also interact with EU.
India: Currently as it stands, in India, there is no legislation or statutory body which specifically deals with online advertising. However, the legislations and bodies which are governing offline ads have the authority to regulate online advertisements also. The Joint Parliamentary Committee (“JPC“) on the Personal Data Protection Bill, 2019 released its report in December 2021. Data Protection Bill, 2021 (“Bill‘) incorporating the amendments and omissions was released where:
Clause 17 provides users with the right to confirmation and access; Clause 18, user may demand erasure of personal data which is no longer necessary for the purpose for which it was processed; Clause 20 applies when a user wants to withdraw consent of data use; Clause 50 The European Data Protection Board has adopted guidelines has been suggested as a guideline.
It’s so complicated, do we adapt?
Whether it is true or not, we may never know as the intricacies of the devices are not known by the lay user!
There are very simple things we can do to ensure that we adapt ourselves to the onslaught of innovation. We need to be clear on how we go “off the grid” where possible.
This also needs to be coupled with regulators who require to ensure that people understand some fundamentals:
Right to privacy: Rules need to be put in place to protect fundamental right to privacy which can only be violated if the three-prong test of legality, necessity and proportionality stands fulfilled. This must be kept in mind by data fiduciaries while dealing with personal data.
Clear Code of practice and retention policies: Best practices in line with the specific code of implementation specified by the data protection Clause 50. There needs to be clear data retention policies for records management for excessive sharing data.
The onus is on us!
Marketers are also now challenged to balance privacy and effectiveness however, they are mutually exclusive. While it is claimed that the mobile phones are not actively listening, there is a substantial digital footprint left that is enough to connect the dots. It is always good to err on the side of caution in these scenarios and the ownership always lies with us, the users!
In case you missed:
- None Found