MOST READ
IN SPOTLIGHT
The global AI boom increasingly depends on a single geopolitically fragile island, turning Taiwan’s chip factories into one of the most…
The AI infrastructure wave is lifting the most unexpected boats, including the makers of Ajinomoto and toilets, and that’s exactly how…
When you open Twitter (X) today, almost every tweet has this comment somewhere in the thread: “@Grok, is this true?” Now,…
A biotech company chasing the return of extinct species has successfully hatched chicks from 3D-printed artificial eggs, pushing de-extinction science into…
TRENDING NOW
Like there are tricks to enter global festivals, or…
DEEP DIVE
Do you use different versions of the same password for your 300+ social media, app delivery, and shopping accounts? Have you…
India’s EV market is being driven by cheap public vehicles says Satyen K. Bordoloi as he outlines how it could lead…
Nithya Selvaraj goes through the history of telcos, their impact on society and its natural evolution to 5g technology On March…
While everybody is familiar with the evolution of mobile networks, from 3G to 4G and now to 5G, Wi-Fi technology has…
EXPLAINED
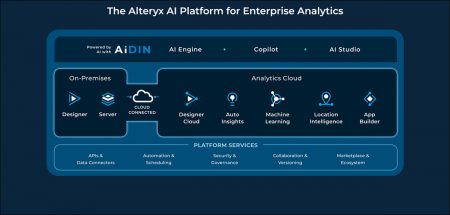
With AiDIN Copilot, Alteryx is not only increasing productivity…