According to Fortinet’s 2026 Cloud Security Report, cloud security teams are more focused on whether their defences can keep up with the speed of change and are less worried about cloud platforms’ security.
As cloud adoption continues to transform security landscapes and IT infrastructure, nearly 88% of enterprises already operate across hybrid/multi-cloud environments. However, a shocking two-thirds lack confidence in real-time threat detection and response capabilities.
These findings point to a growing disconnect between the operational complexity and scale of modern cloud environments and the largely human-driven security processes many enterprises still rely on to defend them. While organisations have invested heavily in securing human identities with behavioural monitoring, access controls, and multi-factor authentication, a seemingly innocuous identity class has largely grown unrestricted: machine-to-machine identities.
IoT (Internet of Things) devices, microservices, service accounts, and API keys now greatly outstrip human users, representing both vulnerability and functionality.
Multi-Cloud – The Default Operating Model
According to Fortinet’s 2026 report, which speaks about closing the cloud complexity gap, it confirms that hybrid/multi-cloud architectures have now become the norm. As cloud environments expand, configurations, identities, and assets change continuously, thus making consistent visibility more difficult to maintain and increasing the attack surface.
This shift to multi-cloud environments has also changed the complexity and scale of identity governance fundamentally. Organisations now manage numerous cloud identities spanning human and non-human users, serverless functions, automated workloads, and service accounts. According to a Harvard Business Review study, the ratio of machine identities to those of humans is around 82:1, making it impossible to operate manual entitlement oversight at scale. Some of the most critical vulnerabilities and challenges of multi-cloud security include:
- Identity sprawl across multi-cloud environments: Enterprises running workloads across multi-cloud environments have no unified view of who holds permissions, need to maintain separate IAM systems, and often face inconsistent access control policies.
- The shift to identity-based security: While traditional on-premises security relies on network perimeters for control access, identities are the perimeter in the cloud. For instance, the 2024 Verizon Data Breach Investigations Report found stolen credentials in nearly 33% of all breaches over the previous decade. This reinforces the idea that identity security is a primary line of defense, and it outranks secondary concerns.
- Compliance requirements: Organisations need to follow global, regional, and local regulations to maintain audit trails, demonstrate access controls, and enforce least privilege across all cloud environments.
- The operational reality of permission drift: With cloud environments changing constantly, deprovisioning lags because automated processes accumulate permissions over time, and new roles are provisioned to unblock deployments. This constant drift creates persistent over-privilege across cloud infrastructure, a risk that needs to be remediated in real-time.

The Rise Of Machine Identities in the Cloud
It’s the shift to CI/CD-driven (continuous integration and continuous deployment) automation and cloud-native architectures that has multiplied machine actors in cloud environments. Even though machine identities massively outnumber human ones, thanks to API-to-API communication, container orchestration, and microservices interactions, most organisations are either not managing them at all or doing so manually.
With service accounts accumulating privileges over the years, tokens rarely expiring, and credentials often hard-coded into storage, these oversights make for a very appealing attack surface for malicious elements. Thus, the idea is that machine identities shouldn’t be merely issued, but rather require monitoring, rotation, and dynamic revoking. Without this discipline in place, scale will turn into a liability.

A State Of Continuous Trust
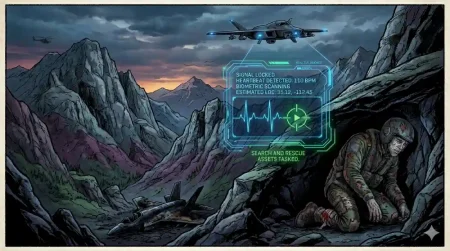
When it comes to AI-driven exploits, legacy patch cycles really can’t keep the pace with them and thus, don’t suit machine identities that might last just mere minutes. Unrevoked API tokens and forgotten service accounts could loiter far longer than workloads that created them, making for the perfect and most vulnerable entry point for malicious entities.
So, what’s the solution to this? It’s continuously validating trust, which blends a number of best multi-cloud practices into a single approach. This translates to reliance on observability-based monitoring with tools such as ELK, Splunk, or Datadog, activating just-in-time controls for workloads, and using ephemeral credentials expiring automatically to catch irregular machine behaviours in real time.
Walmart’s modernisation process also followed this approach, embedding observability and policy-as-code verifications into pipelines and treating machine identities as living entities by validating them at every stage and not assuming trust. The idea is of adaptive trust and questioning each machine identity continuously, making security a living process rather than a compliance milestone.

The Age Of Machine Identities
It’s unlikely that the next phase of breaches come from hacked logins alone. We’re bound to see forgotten API tokens, stale certificates, and service accounts cause havoc, making machine identities the veiled weak link in multi-cloud security. Since we’re entering an identity era where machines are making most of the requests, they demand vigilance equal to, if not more than, human identities.
For organisations, the way forward couldn’t be clearer: treating non-human actors as important citizens of trust, making observability a security tool, and embedding machine identity governance into modernisation projects. When trust adapts to this new reality, the perimeter will no longer be porous and vulnerable to silent breaches, setting the basis for the adaptive, secure infrastructures of the future.
In case you missed:
- Has Private Cloud Made Its Comeback?
- All About Multi-Tenant Cloud Architecture
- The Cloud Cost Conundrum: Is Cloud FinOps the Answer?
- All About Cybersecurity-as-a-Service
- The Rise Of Cloud WAN and SD-WAN: Network For The AI Era
- Blockchain-Based Digital Identity: The Future Of Verification Is Here
- The Rise Of Agentic Cloud – Reshaping Cloud Infrastructure In 2026
- Hiding In The Dark: Navigating The Threat Of Shadow AI
- AI Runtime Security: A Comprehensive Look
- How Zero Trust Works in the Agentic AI Era